The Start[]
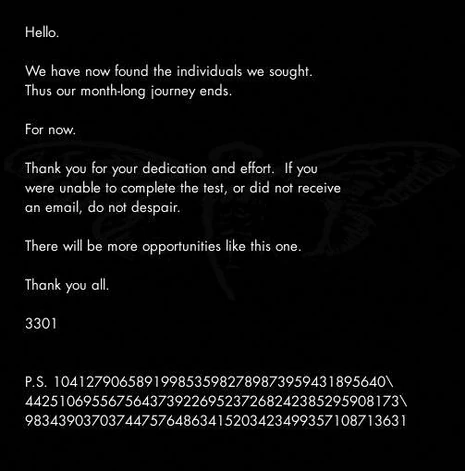
On January 4th, users browsing 4chan's /x/ board were greeted with a mysterious image, unlike much else really seen on that board. It displayed the following message in simple, white-on-black font:
There was almost nobody browsing /x/ at that time who didn't notice it. Many initially thought it was another ARG, some thought it was an NSA recruitment program, and to this day few know where the rabbit hole leads to, and those that do have disappeared from the internet and have not told anybody else any more than they fear to let on.
There is a message hidden in this image
Solvers were quick to try different methods to find it. A common use was to initially open the image file into a text editing application, which allows users to read a dump of the bytes in the image. An unusual text was appended at the end of the file:
TIBERIVS CLAVDIVS CAESAR says "lxxt>33m2mqkyv2gsq3q=w]O2ntk"
This was quickly found to be a Caesar cipher because of the repeated characters, hence the reference. Once deciphered, it read: https://i.imgur.com/m9sYK.jpg
Decrypting this cipher and following the URL led to the discovery of the following image file:
m9sYK.jpg from the Caesar cipher, a hint to use outguess on final.jpg
This was a difficult clue to follow, but solvers soon realized that it meant that the program OutGuess had to be used (hence the words guess and out).
In its simplest form, OutGuess is a steganography program designed to hide messages within images. More on OutGuess can be found at its very own wiki page.
The Message[]
Opening final.jpg in OutGuess led to the following message (concatenated to fit better formatting. The original text can be found here):
Here is a book code. To find the book, and more information, go to http://www.reddit.com/r/a2e7j6ic78h0j/ 1:20, 2:3, 3:5, 4:20, 5:5, 6:53, 7:1, 8:8, 9:2, 10:4, 11:8, 12:4, 13:13, 14:4, 15:8, 16:4, 17:5, 18:14, 19:7, 20:31, 21:12, 22:36, 23:2, 24:3, 25:5, 26:65, 27:5, 28:1, 29:2, 30:18, 31:32, 32:10, 33:3, 34:25, 35:10, 36:7, 37:20, 38:10, 39:32, 40:4, 41:40, 42:11, 43:9, 44:13, 45:6, 46:3, 47:5, 48:43, 49:17, 50:13, 51:4, 52:2, 53:18, 54:4, 55:6, 56:4, 57:24, 58:64, 59:5, 60:37, 61:60, 62:12, 63:6, 64:8, 65:5, 66:18, 67:45, 68:10, 69:2, 70:17, 71:9, 72:20, 73:2, 74:34, 75:13, 76:21 Good luck. 3301
The subreddit in question can be found here.
The Subreddit Code[]
The subreddit contained several text posts and two images, Welcome and Problems? [1]. While the Problems? post was created by the user Reddit u/ImagoOnNib, all others posts were created by u/CageThrottleUs. [2] [3]
At first, only a handful of posts and the "Welcome" image were available. As time when on, more posts regularly appeared and the "Problems?" image was posted. For more information, check out our interactive timeline.
Note : Years later, several deleted posts and another deleted account were found using Reddit's developer API [4].
Cryptographic signatures[]
Each image contained an OutGuess message. Welcome's was this:
It is signed with a PGP signature, a secure method of ensuring that a message originates from a confirmed sender. You can learn more about PGP over at its wiki page.
You can download 3301's PGP key straight from the MIT Keyserver (remember to always check the signature and data against the one available from MIT). Note: in case the MIT server is down, you can download 3301's key here
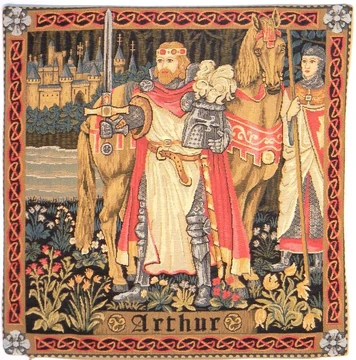
King Arthur references[]
The message embedded in 'Problems?' is:
As expected, it is PGP-signed.
The image depicts a repeating pattern of an "King Arthur" tapestry. Furthermore, trained eyes can see a cup hidden with a autostereogram - given the Arthurian context, it represents the Holy Grail.
Solving the code[]

The subreddit header image
On the subreddit header image, a sequence Mayan numerals can be read. Their Arabic counterparts are: 10 2 14 7 19 6 18 12 7 8 17 0 19
Solvers noticed that the subreddit title, a2e7j6ic78h0j, could be converted to the above sequence by replacing each letter with their position in the alphabet starting with A as 10. Numbers could simply by left as is.
0 -> 0 1 -> 1 ... 8 -> 8 9 -> 9 a -> 10 b -> 11 ...
The subreddit description contained a 23 characters string starting with its name:
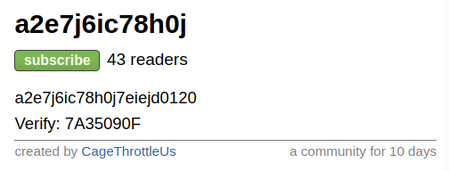
Continuing the conversion process with this new string gave the following sequence:
10, 2, 14, 7, 19, 6, 18, 12, 7, 8, 17, 0, 19, 7, 14, 18, 14, 19, 13, 0, 1, 2, 0
Finally, this sequence can be transformed into a character string by taking the associated letters, starting with A = 0:
kcohtgsmhirathosotnabca
This was found to be the key 'Problems?' mentioned. To decrypt the different text posts, solvers used it as the key of a Vigenère cipher. In short, each letter of the ciphertext should be shifted in the alphabet by an amount of places given by the corresponding value in the key. Characters other than letters (spaces, commas, quotes...) should be left untouched. The shift key is repeated until the end of the line and reset at the start of each new post.
The decrypted text reads: (full text)
King Arthur was at Caerlleon upon Usk; and one day he sat in his chamber; and with him were Owain the son of Urien, and Kynon the son of Clydno, and Kai the son of Kyner; and Gwenhwyvar and her handmaidens at needlework by the window. And if it should be said that there was a porter at Arthur's palace, there was none. Glewlwyd Gavaelvawr was there, acting as porter, to welcome guests and strangers, and to receive them with honour, and to inform them of the manners and customs of the Court; and to direct those who came to the [...]
The text is from The Mabinogion, "The lady of the fountain". The Mabinogion was first fully translated from Welsh into English by Lady Charlotte Guest. 3301's Reddit usernames are anagrams of "Mabinogion" ("ImagoOnNib") and "Charlotte Guest" ("CageThrottleUs").
Later, it was found the key was derived from the King Arthur text: it corresponds to the sequence of first letters of the decrypted text.
The Phone Number[]
Having retrieved the source text, the book code mentioned in the OutGuessed message of the initial image could be applied. In a book code, each letter is encoded with two numbers: a line number and a character index in the line. Applying the book code to the text with the full stops removed gave the following string of text:
Call us at us tele phone numBer two one four three nine oh nine six oh eight
This was a telephone number, specifically (214) 390-9608. This number has since deactivated. Calling this number gave the following message:

Voice On Phone (2012)
Very good. You have done well.
There are three prime numbers associated with the original final.jpg image.
3301 is one of them. You will have to find the other two.
Multiply all three of these numbers together and add a .com to find the next step.
Good luck. Goodbye.
The original image had the dimensions of 509 by 503 pixels, both of which are prime numbers. These were multiplied with 3301 to get 845145127, which gave us http://845145127.com. Note that 845145127 is also in brackets in the PGP key's name.
An archive of the page can be found here: https://cicada-solvers.github.io/845145127.com/countdown_reenactment/[5]
The Website[]
Going to this website led to an image of a cicada and a countdown.
Using OutGuess on the image produced the following message:
When the announced time finally came, the website changed.
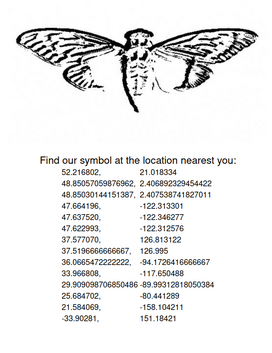
The Global QR Codes[]
The updated website gave a list of coordinates, with seemingly the same cicada image.
Archive: https://cicada-solvers.github.io/845145127.com/coordinates/
However, applying OutGuess on the cicada image produced a different message, containing coordinates. They were the same as what could be found on 845145127.com except for two missing coordinates.
These locations were scattered across the globe, compelling solvers to collaborate. At each of these coordinates, a sheet of paper could be found stuck — in most cases — to a telegraph pole. All posters retrieved had a QR code and an image of a cicada. This was the first appearance of the puzzle logo.
At this point the community realized 3301 could potentially be a global organization of some very talented people, not just a single skilled 4chan user.
The Posters Book Codes[]
Each QR code contained a URL to an JPEG image on 845145127.com, named by 12 digits. For instance, the QR code found in Paris linked to: http://845145127.com/427566844663.jpg. Each image had an overexposed white cicada logo on a black background, along with the text "everywhere" and the group name.
Using Outguess revealed that one PGP-signed message was embedded in them. Two kinds of messages were found:
and
Solvers knew these were book codes along with a description of the book needed. A warning about too much collaboration was also included, saying that only the first few, or the active few, that make it to the end will receive entry.
Agrippa[]
A poem of fading death, named for a king
Meant to be read only once and vanish
Alas, it could not remain unseen.
By typing in keywords from its description, solvers were led to the poem Agrippa. Applying the book code (and interpreting literally the product of the first two primes) produced:
sq6wmgv2zcsrix6t.onion
This was the address of a hidden service on the Tor network, a anonymity-oriented communication network. Visiting this page with an adequate browser, solvers found the following message along with an email form:
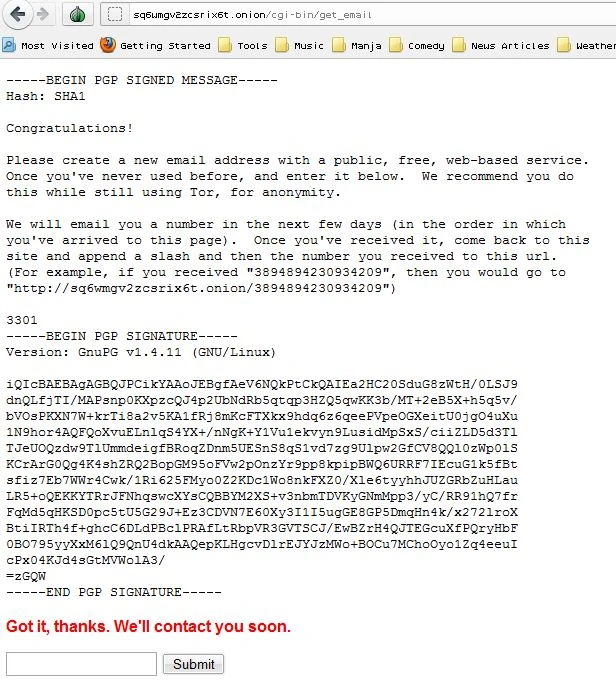
sq6wmgv2zcsrix6t.onion (source code prior to submission)
After submitting an email address, a message told solvers to patiently wait: "Got it, thanks. We'll contact you soon."
Encyclopædia Britannica[]
In twenty-nine volumes, knowledge was once contained.
How many lines of the code remained when the Mabinogion paused?
Go that far in from the beginning and find my first name.
Back in 2012, it is unclear whether some solvers knew how to solve this book code. If some did, nothing was properly documented and a most of the community wasn't aware of it [6] [7]. Still, they thought the description given referred to the "Encyclopædia Britannica", 11th Edition[8].
On 6th January 2012, no posts were made to the r/a2e7j6ic78h0j subreddit for about 24 hours. After this period, encrypted text lines have been once again posted about every 6th or 7th hour.
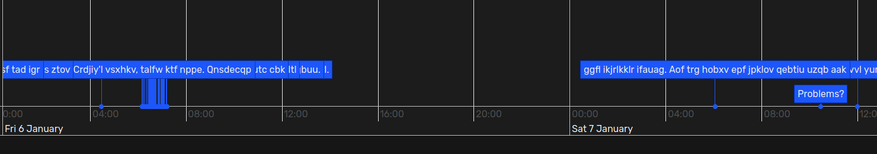
A chronological view of the 24 hours pause - Interactive version
Before this pause, 76 lines of ciphertext have been posted. The Mabinogion book code used the first 65 lines, in sequence:
[...] 68:10 69:2 70:17 71:9 72:20 73:2 74:34 75:13 76:21
So, when the Mabinogion paused, 11 lines of the code couldn't yet be resolved and remained. This hinted solvers to use the 11th Edition of the Encyclopædia Brittanica.
"my first name" referred to the word "cicada". When applied to the "Cicada" article of the encyclopedia, the book code revealed another onion address. However, the formatting from the "Project Gutenberg" transcript had to be used and the first line had to be skipped (equivalent to using a 0-based numbering).
eq6emgv2ehsrix6t.onion
Note: this is the only instance where 3301 referred to themselves as "Cicada".
Unfortunately, this hidden service is long gone. It is thought to have hosted a similar email form as could be found the Agrippa onion address. Again, whether it was accessed by someone in 2012 is unclear. The rest of this wiki page will thus refer to the Agrippa onion address.
The RSA Emails[]
Those who applied early enough were greeted with an email giving them a number. Following 3301's instructions, they went to "sq6wmgv2zcsrix6t.onion/NUMBER". A similar message to this one appeared:
Everyone received a different 'n' value and a different RSA encrypted message. Of course, the "Identity" field would also be different. [9]
A mention of the "Numbers dot TK" hint made people that didn't receive an email aware — presumably through leaks — of the existence of a second chance. Around the same time, the 845145127.com website changed. To know more about The Second Chance, see The second chance (2012).
Regarding publicly shared keys or messages, their owner would be emailed the following message by 3301:
The RSA puzzle[]
To crack the RSA encryption, people had to factor their n — the modulus — into its two prime factors. In general this factorization is too computationally expensive, but the modulus being small made it possible (it has a low bit modulus and is therefore breakable). Decrypting the message could then be possible using a simple perl script.
For the above message, n factors into 80411114232571782218163489375797613948878398942588985417 and 98007492061325958997349177934627388613835953553459586261. To determine these factors, solvers had to use tools such as factmsieve, letting them run for a few hours. The decrypted message is[10]:
33521494043430258676
Submitting the correct answer to the same onion initially resulted in a 500 error, however on the 17th January at around 2:49 UTC, it instead reported:
A screenshot of the 500 Internal Error initially shown
Correct. We’ll email you.
The MIDI puzzle[]
As promised, 3301 sent an email telling people to go back their 'sq6wmgv2zcsrix6t.onion/NUMBER' page. The page now had a message unique to each participant.
The large 'PGP MESSAGE' block differed in each message. It is a PGP-signed binary file named 'Cicada.mid'. To extract it, the message must in the first place be isolated and the leading "- " on the armor headers should be removed. The file is then decrypted using:
gpg --decrypt message.txt > Cicada.mid
The resulting file is a MIDI music file. It contains of two songs, but neither of them sound to be real music pieces.
The poem included in the PGP-signed message is the "Chorus" from William Blake's poem A Song of Liberty
It was noticed the second music track encodes the poem. A MIDI file describes the presses/releases of instruments keys; thus, each tone played has a defined note (encoded as a number) and a duration. Each (note, duration) pair played could then be associated with a letter given by the poem:
Note played | Duration | letter ================================= 48 | 96 | l 49 | 24 | e 48 | 192 | t 48 | 192 | t 55 | 24 | h 49 | 24 | e 55 | 96 | p 44 | 192 | r 43 | 96 | i 49 | 24 | e 46 | 192 | s ... | ... | ...
In short, the second MIDI song was a substitution cipher where each note played corresponded to one letter. Once the full substitution table has been created, the rest of this second song can be decrypted. It simply repeated the Chorus two more times.
Following 3301's hint (Let the Chorus be your guide), the same substitution table was tried on the first track. Unfortunately, this resulted in a failure as almost no notes were in common.
Using frequencies analysis on the (note, durations) pairs, or by noticing that early letters in the alphabet were associated with shorter durations, a new substitution table can be crafted. Alternatively, this is equivalent to shifting up all notes in the previous substitution table by an octave (which equates to an addition of 12). This could have been hinted by 3301 ("...your guide to the depths"), as the second song was lower-pitched.
However, 3 characters weren't in the poem: q, x and z. But the substitution table can naturally be completed:
(note, duration) | letter ============================== (55, 24) | a (56, 24) | b (58, 24) | c (60, 24) | d (61, 24) | e (63, 24) | f (65, 24) | g (67, 24) | h (55, 96) | i (56, 96) | j (58, 96) | k (60, 96) | l (61, 96) | m (63, 96) | n (65, 96) | o (67, 96) | p (55, 192) | q [*] (56, 192) | r (58, 192) | s (60, 192) | t (61, 192) | u (63, 192) | v (65, 192) | w (67, 192) | x [*] (55, 384) | y (56, 384) | z [*]
Decrypting the first song results of the above MIDI gives :
verygoodyouhaveproventobemostdedicatedtocomethisfartoattainenlightenmentcreateagpgkeyforyouremailaddressanduploadittothemitkeyserversthenencryptthethefollowingwordlistusingthecicadathreethreezeroonepublickeysignitwithyourkeysendtheasciiarmouredciphertexttothegmailaddressfromwhichyoureceivedyournumbersyourwordsaremuscledroppumpkneebirdwatchbellballhammerpockethookhousebrakefeatherknotticketboatboxmooncloudbulbcarriageboxtraysquarecupstationmatchtoothovenhorsepenciltraycollartreescissorsbrushdrawerbrickarmenginesockumbrellasheepapplehornhatchainforkscrew
Finally, after properly formatting the text:
Very good. You have proven to be most dedicated to come this far to attain enlightenment. Create a GPG key for your email address and upload it to the MIT key servers. Then, encrypt the following word list using the Cicada 3301 public key, sign it with your key. Send the ASCII-armoured ciphertext to the Gmail address from which you received your numbers. Your words are: muscled drop pump knee bird watch bell ball hammer pocket hook house brake feather knot ticket boat box moon cloud bulb carriage box tray square cups station match tooth oven horse pencil tray collar trees scissors brush drawer brick arm engine sock umbrella sheep apple horn hat chain fork screw
Each MIDI file contained 50 unique words. Running the following commands outputted the PGP-signed message which could then be sent.
gpg --gen-key # Key generation gpg --keyserver pgp.mit.edu --send-key [KEY_ID] # Upload the key to be MIT keyservers gpg --armour --default-key [EMAIL] --sign --encrypt # Encrypt the words
The Invitation[]
Those who sent an encrypted PGP signed email with their words received at around Monday, February 6th an email informing them that there would be no more puzzles. It also gave directions to log on to a Tor hidden service, with a given username and password. Around the same time, they were invited with the infamous "leaked email".
From here, nobody knows what really happened, as the original puzzle was not very well documented in its end stages like the second puzzle was. Hopefully one day this will come to light, but after receiving this email every person that did so went completely dark, as if they had disappeared from the internet.
Nobody knew how deep the rabbit hole went, but all the solvers could agree: it was the deepest they'd ever seen.
What happened after this is mostly still not known, apart for few slips when some people told a bit more about what was going on later. Logs of those testimonies can be found on Unfiction. Legitimacy of those is not confirmed, it might be just trolling. After all, 3301 might not exist at all.
The Final Message[]
After a whole month without any word from 3301, the following message was posted on the subreddit from the start (r/a2e7j6ic78h0j), in a post entitled Valēte! (meaning goodbye, farewell).
A PGP-signed version of the message was embedded in the image using Outguess. A noteworthy observation is the presence of space sequences of prime length, similarly to what could be found in other 3301 messages. These have yet to be explained.
Excepted for The Leaked Email or the "Necrome" message, this was the last known PGP-signed message received from 3301 in 2012.
In programming or mathematics, backslashes are commonly used to signify that a number continues on the next line. The P.S. message has not been used to date despite its factorization into 99554414790940424414351515490472769096534141749790794321708050837 and 104593961812606247801193807142122161186583731774511103180935025763.
Mentions of 3301 popped up throughout the rest of the year, and by December everyone had forgotten about the puzzle... Until 2013.
Note: For any of the fake messages/speculations, please visit the appropriate pages.
| |||||||||||
Other links[]
Nox Populi has a multi-part series on what happened in 2012 (parts one, two, and three) that we recommend you watch.
To better understand how the puzzle unfolded, you might find our timeline tool useful.
Here are other links that explain these steps of the puzzle in different ways that you may find helpful:
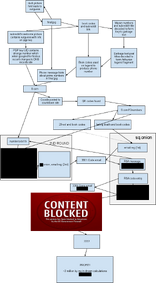
Diagram of 2012 puzzle
- https://github.com/scream314/cicada3301/blob/master/2012.md
- https://web.archive.org/web/20160814151608/http://bernsteinbear.com/blog/cicada/
- http://www.clevcode.org/cicada-3301/
References and notes[]
- ↑ Nowadays, the image's Imgur page contains a Portuguese title. It describes how this image is part of the 2012 Cicada 3301 puzzle.
Archive of the image without the title
It's thought to be the result of the image getting cross-posted on Reddit. - ↑ The post entitled Valēte! marked the end of the 2012 puzzle. It wasn't available when solvers first discovered this subreddit and is not yet relevant.
- ↑ All posts excepted Problems?, Welcome, Valēte! and the first two ciphered posts end with a carriage return (
\n) character. - ↑ The deleted posts are :
- A first version of the "Problems?" post. The image posted did not embed any stenographically hidden data, which may explain why it was removed and replaced by the well-known post. This post was made by a deleted account.
- The second and third encrypted posts were reposted soon after posted by a deleted account. These newer posts were removed to keep the ones from u/CageThrottleUs.
There also exists a deleted "Welcome" post from 2015, however it is believed to be unrelated.
- ↑ We only have a partial archive of
845145127.com; the cicada image with the correct outguess message is long lost. For more information, read our archival repository. - ↑ tekknolagi's blog doesn't mention it
- ↑
[2013-01-13 18:19:21] <Lurker69> http://pastebin.com/HcLcAeYW [2013-01-13 18:19:31] <Lurker69> this is part of last years puzzle and it is legit [2013-01-13 18:19:36] <Lurker69> was never solved [2013-01-13 18:19:52] <Lurker69> book is ptobably encyclopedia brittanica... [2013-01-13 18:20:04] <Lurker69> but nobody knew which version [2013-01-13 18:20:10] <soulseekah> interesting... [2013-01-13 18:20:28] <soulseekah> yet people finished the game without solving it right? [2013-01-13 18:21:23] <soulseekah> "You've shared too much to this point. We want the best, not the followers." yet this year they encouraged teams right/
- ↑ See https://clevcode.org/cicada-3301/, the last 5 paragraphs
- ↑ This pastebin is believed to contain an another instance of such message. However, it was censored and the original message has yet to be found. The first censored field is eJwBzQAy, and n is 7467492769579356967270197440403790283193525917787433197231759008957255433116469460882489015469125000179524189783.
Similarly, this pastebin and a n0v4 wiki archive are another instances of (censored) RSA messages. - ↑ In these IRC logs, a solvers leaks what he claims to be legitimate numbers from this step:
33407224003429952528,07088751691164076086